What Is IT/OT Convergence? A Practical Guide for Plant Teams
- Sep 14, 2025
- 5 min read
Executive Summary
IT/OT convergence aligns machines, PLCs, robots, and SCADA (operational technology) with networks, databases, analytics, and cloud (information technology) so production decisions rely on a single, trustworthy data spine. When executed via a data-ops layer—such as Artisan Edge—plants can increase throughput, reduce unplanned downtime, and accelerate changeovers without rip-and-replace projects. This guide provides the business case, a brownfield-friendly reference architecture, a 30-day rollout plan, a governance checklist, and acceptance criteria to ensure value realization.
Table of Contents
What is IT/OT Convergence?
Why It Matters: Business Impact & KPIs
Reference Architecture (Brownfield-First)
The 30-Day Start Plan (Week-by-Week)
Governance: Namespaces, Models, and Security
Implementation Checklist
Risks & Mitigations
What “Good” Looks Like: Acceptance Criteria
FAQs
Next Steps & Call to Action
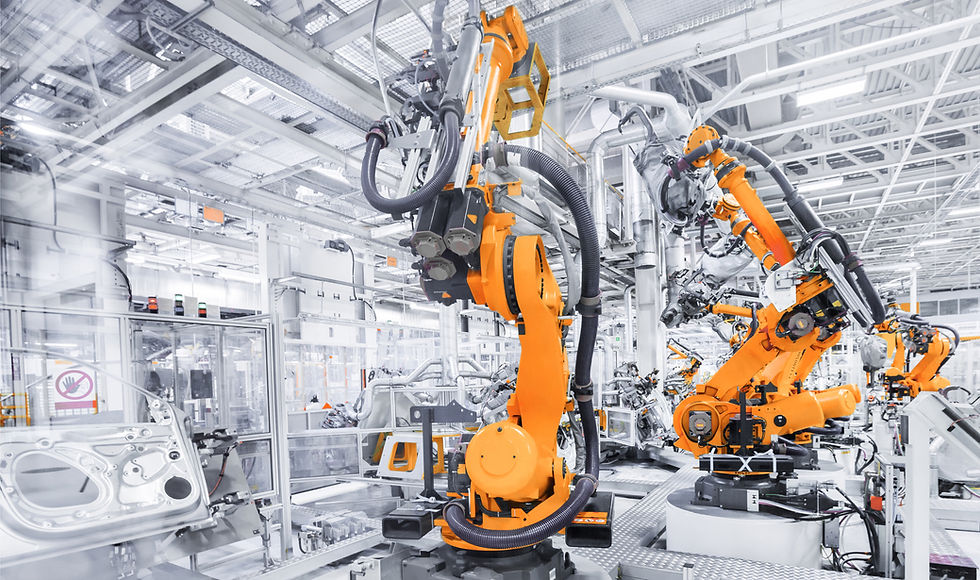
1) What Is IT/OT Convergence?
Definition: IT/OT convergence is the disciplined alignment of operational systems (PLCs, SCADA, historians, robots, sensors) with enterprise information systems (networks, databases, analytics platforms, cloud) to deliver reliable, timely, and contextualized production data to the right people and applications.
Core characteristics
Unified data model: Common naming, units, and state definitions across lines and sites.
Event-driven distribution: Publish/subscribe patterns (i.e., MQTT Sparkplug) reduce brittle point-to-points.
Standards-aware connectivity: OPC UA for structured asset access; MQTT for scalable telemetry and events.
Data lineage: Transparent mapping from raw tags → engineered metrics → KPIs.
Security & governance: Identity, segmentation, encryption, and change control across OT and IT.
Artisan Edge’s role: The data-ops backbone that normalizes tags, enforces topic standards, and orchestrates event pipelines into OEE, CMMS, and analytics—coexisting with your SCADA and HMI.
2) Why It Matters: Business Impact & KPIs
Convergence is not an academic exercise; it moves the needle on plant economics.
Financial & operational outcomes
Throughput & OEE uplift: Real-time, trusted signals enable proactive interventions on Availability, Performance, and Quality.
Downtime reduction: Context-rich alerts flow into CMMS within minutes, trimming MTTR and preventing repeat failures.
Faster changeovers: Parameter libraries and verified recipes reduce scrap and trial-and-error during SKU swaps.
Consistent reporting: A single semantic model eliminates “multiple truths,” improving auditability and decisions.
Scalable rollouts: Standard interfaces avoid re-plumbing every time you add a new line, app, or site.
Indicative KPI improvements (pilot targets)
Alarm nuisance rate ↓ ≥50% (via hysteresis and proper state modeling)
Mean alarm acknowledgment time ↓ ≥30%
OEE variance vs. manual checks ≤1%
Alert-to-CMMS work order SLA <5 minutes with correct asset context
3) Reference Architecture (Brownfield-First)
3.1 Layered view
Layer | Purpose | Technologies | Notes |
Cell/Line (OT) | Sense/control, machine states | PLCs, robot controllers, drives, sensors | Keep safety-critical control local. |
Edge Connectivity | Normalize and distribute signals | OPC UA (browse/semantics), MQTT Sparkplug (pub/sub) | Include buffering & store-and-forward. |
Semantic Data Layer | Canonical names, units, states; lineage | ISA-95 asset/process model; tag normalization | Prevents duplicate truths; enables cross-app reuse. |
Apps & Integrations | OEE, alarms, traceability, CMMS | Dashboards, APIs, work order creation | Use event-driven pipelines with SLAs. |
Security & Governance | Access, segmentation, change control | mTLS, ACLs, RBAC, audit trails | Treat topics/namespaces as productized interfaces. |
3.2 Protocol roles (OPC UA vs MQTT Sparkplug)
OPC UA: Client–server access for browsing device address spaces and invoking methods. Best close to equipment and vendor tools.
MQTT Sparkplug: Publish/subscribe for scalable, state-aware distribution across apps/sites. Great for telemetry, alarms, and backhaul.
Typical pattern: OPC UA in the cell, MQTT Sparkplug at site/enterprise level. Artisan Edge bridges the two while enforcing a canonical model.
4) The 30-Day Start Plan (Week-by-Week)
Week 1 — Objectives, Inventory, Standards
Select 1–2 bottleneck lines; define three KPIs (i.e., unplanned downtime, FPY, changeover time).
Inventory OT assets: PLCs/robots, protocols, tag counts, network paths.
Draft naming & topic standards and retention SLOs (i.e., hot 30 days, warm 12 months).
Identify data owners and approve a minimal governance charter.
Week 2 — Minimal Viable Connectivity
Deploy an edge broker/gateway with OPC UA + MQTT Sparkplug.
Publish 20–40 high-value signals per line under disciplined namespaces (i.e., site/area/line/cell/metric).
Enable store-and-forward; validate lossless behavior in planned disconnect tests.
Establish time synchronization (NTP/PTP) and log time bases for lineage.
Week 3 — Model, Dash, and Alert
Normalize tags to a canonical schema aligned to ISA-95 (equipment, materials, processes).
Build a first OEE dashboard with visible data lineage (source tags/topics → formulas).
Implement alarm policies with hysteresis and deadbands to suppress chattering; target ≥50% nuisance reduction.
Run operator walk-throughs; capture usability feedback.
Week 4 — Close the Loop & Resilience
Integrate to CMMS: auto-create work orders with asset, threshold reason, and recent signal context.
Conduct a failover drill (broker restart, WAN loss); record freshness, loss, and recovery metrics.
Hold a go/no-go review: KPIs, data quality gates, and next-line replication plan.
5) Governance: Namespaces, Models, and Security
5.1 Namespace & naming discipline
Adopt a strict pattern such as:
site/area/line/cell/asset/metricRules
Lower-case; underscores for readability; SI units; explicit states (run, idle, fault, changeover).
Versioned schemas and topic contracts (treat as APIs); lint for violations before deployment.
5.2 Semantic modeling (ISA-95 aligned)
Equipment model: Sites → Areas → Lines → Cells → Assets.
Material model: Item master, lots/serials, genealogy relationships.
Process model: Steps/recipes with parameter libraries and tolerances.
5.3 Security & access control
Zones and conduits: Segment OT from IT; restrict east-west movement.
Mutual TLS and broker ACLs; rotate certs, enforce least privilege.
Secrets management: No embedded credentials in PLC logic; centralized rotation.
Audit trails: Changes to schemas, topics, and alert rules recorded and reviewed.
6) Implementation Checklist
OT asset & communication map (owners, endpoints, protocols)
Topic & naming standard published; ownership assigned
≥ 40 high-value signals streaming with buffering and retry
ISA-95 model in place; units & enumerations standardized
OEE dashboard live; lineage documented
Alarm rules tuned (false positives <10%)
CMMS integration live; alert → work order <5 minutes
Failover drill results logged and remediation items closed
7) Risks & Mitigations
Point-to-point fragility:
Replace bespoke extracts with pub/sub and reusable data contracts.
Namespace sprawl:
Enforce linting, code reviews, and ownership before topics go live.
Security drift:
Certificate rotation, RBAC, and periodic access audits; segregate admin from data paths.
Pilot purgatory:
Executive sponsor + operator champion + pre-agreed KPIs and exit criteria.
Duplicate truths:
Maintain a single semantic model; forbid app-specific aliases.
8) What “Good” Looks Like: Acceptance Criteria
Freshness: ≥ 98% of critical topics within SLO; loss <0.01% across outages.
Accuracy: OEE dashboard variance vs manual audit ≤1%.
Responsiveness: Mean alarm acknowledgment time ↓ ≥30% vs baseline.
Workflow closure: Alert → CMMS work order <3 minutes with correct asset context.
Scalability: Adding a new line/app requires configuration, not bespoke code.
9) FAQs (Schema-Ready)
Q1. Do we need to replace SCADA or historians?
No. The data-ops layer coexists with SCADA/HMIs. It normalizes and routes signals while SCADA continues to handle visualization and control.
Q2. How do we handle legacy protocols?
Use edge gateways to translate proprietary or serial interfaces into OPC UA and MQTT. Start with the highest-value tags and expand iteratively.
Q3. How do we measure success?
Pick three KPIs tied to cost or revenue (i.e., unplanned downtime, FPY). Add data lineage audits and quarterly failover drills.
Q4. Is cloud required?
Not for control. Use edge for low-latency control, buffering, and survivability. Use cloud for cross-site analytics and model training (see Edge vs Cloud framework).
Q5. Can we mix OPC UA and MQTT?
Yes—this is often optimal: OPC UA near equipment for structured access; MQTT Sparkplug for scalable, state-aware distribution.
10) Next Steps & Call to Action
Book a 30-minute IT/OT mapping session. We will inventory one line, propose a namespace and ISA-95 model, and outline a 30-day plan tailored to your plant.
Schedule time with us here:

Comments